Before discussing the best obfuscation VPN in 2023, let’s discuss a few things first…
A VPN creates a link between two endpoints. It serves a way to secure communication by encapsulating data into a virtual tunnel that prevents any third-party from checking the destination address or the type of data flowing through.
Commercial VPNs provide this functionality in an easy-to-use manner. A user simply has to download an app that connects to the service and start browsing the web. VPNs are the go-to way to unblock websites. But the fact that it bypasses the restrictions comes at the chagrin of the Internet Service Provider (ISP) or the government that has put them in place.
ISPs have upgraded their tools to detect VPN traffic to block it; this is where obfuscation comes in. Obfuscation refers to the technique of disguising VPN traffic as normal web traffic so that it can bypass stringent firewall checks on the ISP’s end. I’ll discuss that in a moment, and also how exactly that is achieved when VPN is a quite a sophisticated tool already that involves tunneling and strong encryption
Why Obfuscation is Needed
The burning question immediately might be why such techniques are required just to browse the web. In a perfect world, the internet is a resource available to everyone in its entirety. It means unrestricted access from anywhere in the world and without any special charges for certain types of content, such as streaming Netflix.
Freedom of speech remains ostensible for some countries of the world. Certain countries, such as North Korea and China, completely control the narrative that leaves the country. They do so by controlling the internet itself; by limiting access to the online world. That’s not saying that the internet is not available in these countries, but it’s severely controlled and many popular websites remain blocked from access inside the country.
To give you an idea, here are some of the websites blocked in China:
- YouTube
- Netflix
- DailyMotion
- Wikipedia
- TikTok
- Twitch
- Vimeo
- Discord
- Bloomberg
- The New York Times
- Reuters
This is just a handful of websites that are inaccessible. These are some of the top social and entertainment platforms, and the list doesn’t end there.
China’s firewall is dubbed as the Great Firewall of China. The firewall is a piece of the puzzle that makes up the country’s digital surveillance infrastructure. Internet Service Providers (ISP) and telecommunication authorities are mandated to record the activities of every user. Here are some countries that have banned or allow limited use of VPN:
- China
- UAE
- Iran
- Iraq
- North Korea
- Turkey
- Oman
- Russia
- Egypt
Deep Packet Inspection is one technology that allows internet service providers to about what kind of traffic a user is sending. Let’s discuss DPI to understand obfuscation better.
What is Deep Packet Inspection
Internet communication involves a series of exchanges between the sender and the destination. Data is broken into packets and sent in a series with a header on each packet to identify things such as the source and destination IP address. Think of a packet as a mail that has the delivery destination information, but the contents of the letter are concealed in the envelope. Like a mailman, the ISP simply checks the header and forwards the packet to its destination.
Using Deep Packet Inspection is akin to looking inside the envelope. Normal packet inspection techniques only allow the ISP to read the header, but DPI enables it to inspect the payload itself.
DPI adheres to the rules that have been set by the ISP. So if the ISP has blocked certain websites, then it can do so by looking at the content and blocking access.
The technique only works for packets that are not encrypted. By leveraging HTTPS, most websites today use encryption to make user sessions private by authenticating and securing the connection first with a handshake that happens with a digital certificate. It’s easy to see which websites are secure. Notice the padlock icon next to the URL address bar; it means the website and your device are communicating securely.
ISPs can still use DPI by faking as a certificate authority, but that’s a cumbersome and resource-hungry process. Encryption has pretty much prevented snooping from the ISP.
How Obfuscation Works
Internet communication is predictable to a certain degree. Communicating requires a destination IP address and a port number that’s defined by the application. Regular HTTP web traffic uses port 80, SMTP traffic uses port 25, for example.
An obfuscated VPN camouflages the traffic as HTTPS traffic by using port 443 as that’s the port used by the protocol. If the ISP was to block that port, then it would be breaking the web access for you.
So, why not just use a VPN in its raw form if encryption prevents DPI? Well, because VPN has some known patterns, including the IP address of VPN servers that may be known and the port numbers that are commonly used by VPN. Hence, these ports or the IP addresses can get blocked in countries that frown upon the use of VPN services.
VPN protocols such as OpenVPN can run on Port 443, allowing it to pass in stealth mode through the firewall. Obfuscation is special and requires that the VPN service is offering it. It is similar to Double VPN in terms of features that VPN providers offer. Where Double VPN passes your data through multiple VPN servers, and obfuscated connection will allow the VPN traffic as web traffic.
DPI is not an evil technique. It entirely depends on what it’s being used for. Using DPI to ensure that data packets don’t contain malware is a legitimate way to ensure that security of the network is not compromised. But like many other technology, it can be used for an ill-purpose.
VPN Services with Obfuscated Servers
You may ask yourself that if OpenVPN can run on a different port, then why does the question of which VPN services can run obfuscated exist?
Because DPI can detect packet type and block it even if it’s coming from a port not typically used by VPNs, a VPN service has to implement a customized server based on the OpenVPN protocol to hide its known signatures. Hence, you can’t simply connect to a VPN service using the OpenVPN protocol and expect things to work or not get caught.
Remember, using a VPN is prohibited in some countries such as China and the United Arab Emirates (UAE). So, it’s of utmost importance that you hide your activities AND that you are using a VPN. It may land you a fine if you access blocked websites through a VPN.
Obfsproxy is one of the ways to mask OpenVPN traffic. OpenVPN Scramble is another method that relies on XOR cipher to encrypt OpenVPN traffic to hide OpenVPN’s known encryption pattern. However, the implementation may be different between each VPN service, you only need to pay attention to the availability of the feature. Below are some of the VPN services confirmed to feature obfuscation.
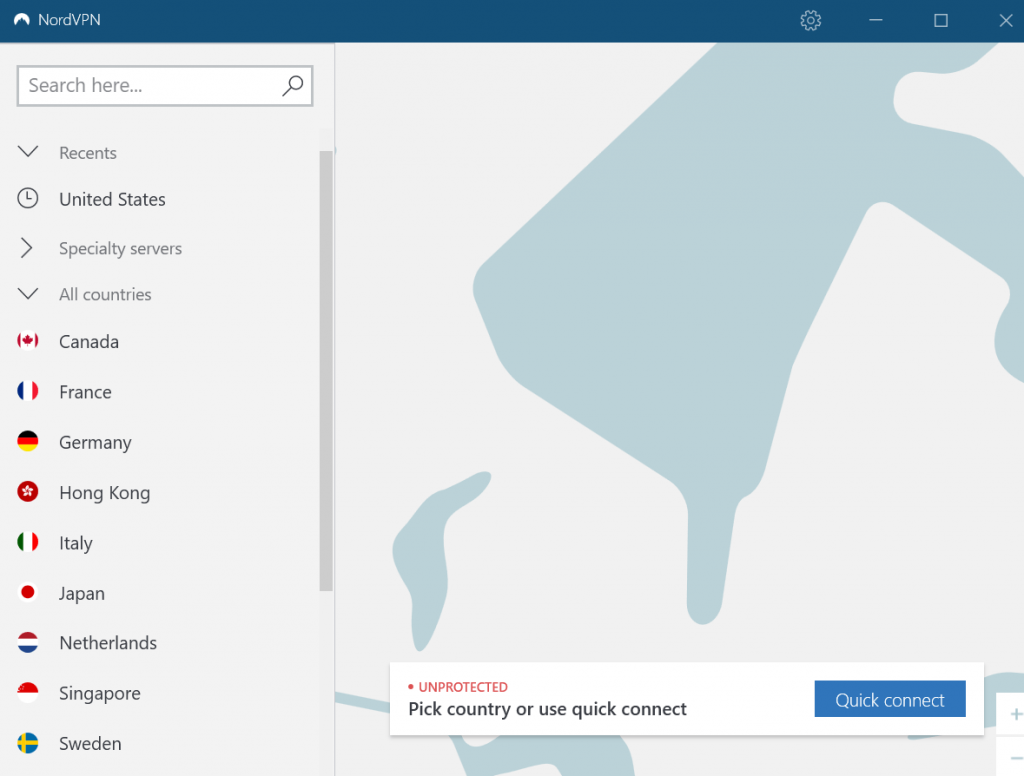
NordVPN
As one of the leading VPN services that have one of the largest global VPN server network, NordVPN has a separate selection of obfuscated servers. It’s not immediately visible in the UI, so you’ll need to enable in the Settings. Once you toggle the switch in Advanced settings, obfuscated servers will appear in the VPN server list.
In the mobile version of NordVPN, go to Speciality Servers to select obfuscated servers.
Since obfuscated servers is a different list, you won’t be able to enjoy the long-list of servers you’ve come to expect from NordVPN. However, not everyone will be jumping to them, so the servers are not likely to experience the kind of traffic the normal VPN servers do.
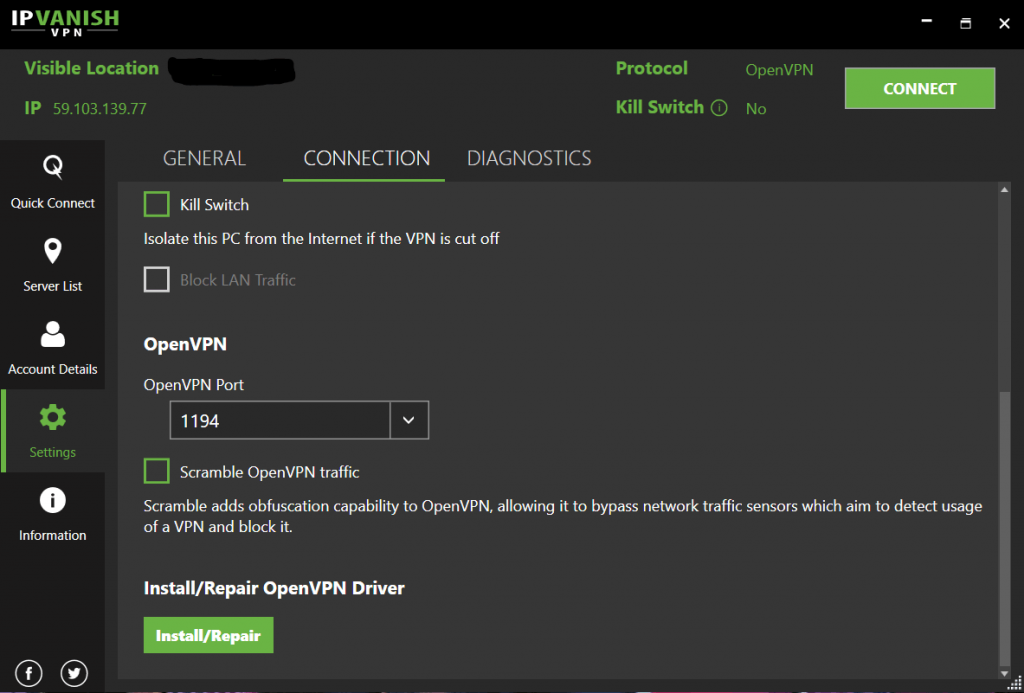
IPVanish
IPVanish uses OpenVPN Scramble to hide the traffic. Like NordVPN, it’s also not immediately visible in the UI. Go to Settings from the left sidebar, switch the Active Protocol to OpenVPN under Connection then check the Scramble OpenVPN traffic.
The option is only available for Windows, Android, and FireTV versions of the app. The iOS app does not support scrambling because it does not use the OpenVPN protocol; IKEv2 and IPsec are the only protocols available in the iOS version.
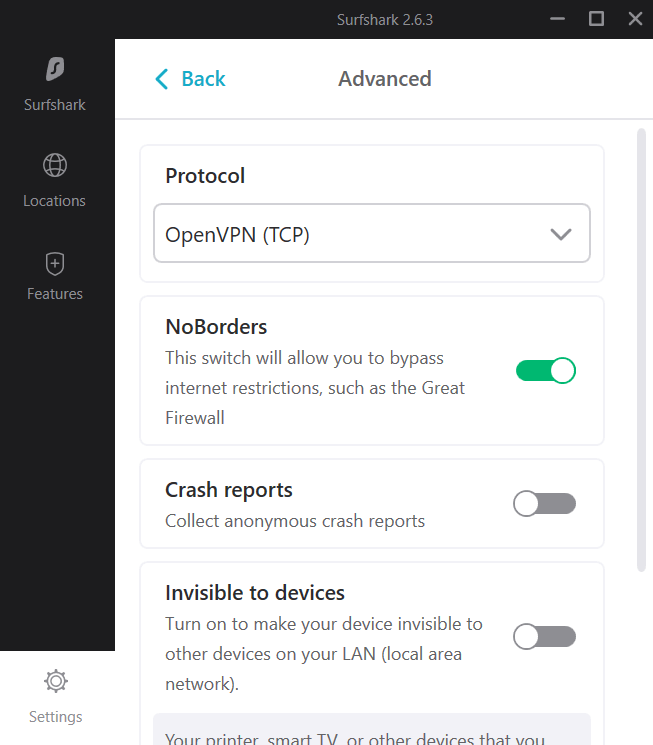
SurfShark
SurfShark has implemented a simple way to hide your traffic. Open the app, click on Settings, select Advanced, then ensure the No Borders option is turned on. Now you are free to connect to any server in countries where VPN is restricted.
FastestVPN
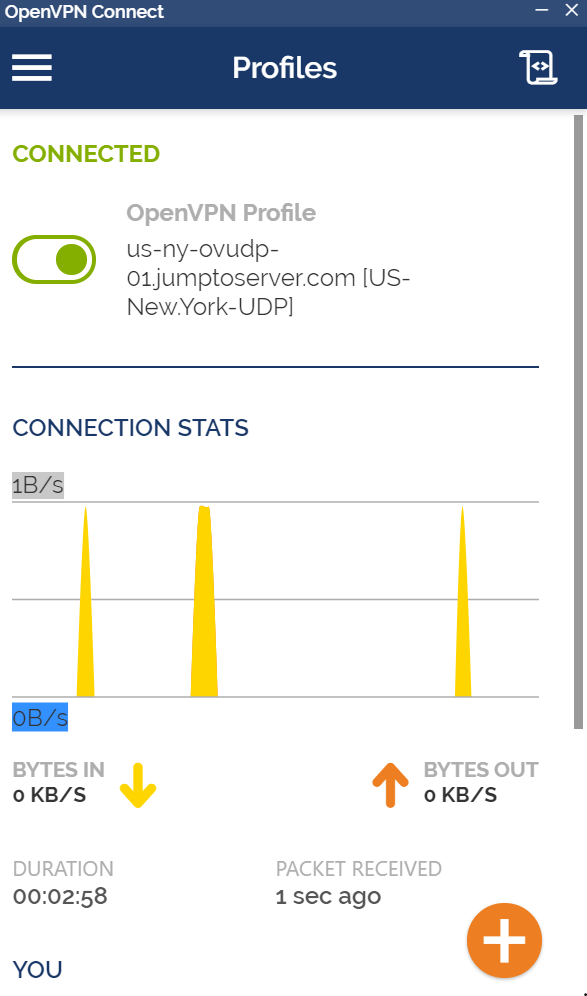
FastestVPN does not feature any obfuscated servers. However, the customer support told me that the VPN works in the UAE and China, but not through its app. You’ll have to download the OpenVPN client first, then use FastestVPN’s OpenVPN server config file to browse the web in restricted countries.
It does not appear to be obfuscation, so we would recommend caution using FastestVPN in a restricted country until the service rolls out the feature officially to its app.
First, download the OpenVPN client from here. Then head over to FastestVPN’s server page and download the OpenVPN config file of the server of your choice. The server has to be of a region outside of the region you want to unblock. Otherwise, you can’t bypass restrictions.
There is a handy tutorial with visual aids by FastestVPN. There are tutorials for other platforms as well, check them out here.
These are some of the VPN services I was able to confirm that have obfuscated servers. Some other VPN services offer it, but as always, I like to stick with our list when it comes to recommendations. The list we have curated for you at the Top VPN Service considers several factors, not just obfuscated servers.
Conclusion
That wraps up obfuscated servers. VPN is a complicated subject; it encompasses several technologies to make a smooth and consistent experience possible, not to mention a private connection. It’s remarkable how we can navigate through these technologies thanks to the VPN services and their user-friendly interfaces. Otherwise, creating an obfuscated server is something that requires considerable knowledge.
I would advise strict caution. Always read up on local laws wherever you travel. If there are cracks in the VPN service’s obfuscation method or the infrastructure has been upgraded, then the risk of viewing blocked content is not worth paying hefty fines. It also depends on the type of content you are viewing. For example, pornographic websites are entirely banned in Middle Eastern countries.
As long as you’re not doing something illegal through a VPN, you should be fine.



Leave a Reply